How to Stay Safe on the “Dark Web”
A frequent question asked about the dark web is how to “stay safe” on it, and the answers often go in the direction of sensationalism, as in “There's NO WAY to stay safe on the dark web! Just don't go on it!”
In reality, the dark web is not that much more dangerous than the clearnet – in fact, the opposite may be true, depending on what you do with it. If it is Tor you're referring to, then it is designed to be more secure, so that is an advantage to start off with.
The part of Tor that may be risky is that there are numerous phishing sites and scams on it, as well as things like child abuse material. If your intention in using Tor is just to look around, then you probably do not need to worry about getting scammed. On the other hand, if you are looking to purchase things, such as drugs or hacked accounts, this is where many people lose money or get their information stolen.
To avoid the phishing sites, use a reliable link list like dark.fail (darkfailenbsdla5mal2mxn2uz66od5vtzd5qozslagrfzachha3f3id.onion), which has PGP-verified links for darknet markets and some other sites, like forums. At present, this site is generally considered to be the most reliable source for onion links, though Darknet Live (darkzzx4avcsuofgfez5zq75cqc4mprjvfqywo45dfcaxrwqg6qrlfid.onion) is a close second.
Another question that gets asked frequently is what operating system you should use. Contrary to popular belief, it does not matter as much as one might think. While Windows is certainly more vulnerable to malware, there is just as much malware on the clearnet as there is on Tor. There are, however, some sites that have PDF files and other sorts of files that may contain unsafe code. This is where using your good judgment becomes handy.
If you are concerned about operating systems, some Linux distros are designed with security in mind, such as Tails, Qubes, and Whonix. Tails, for instance, is amnesic, i.e. you can run it as a VM on a USB drive and then delete everything after the session is finished.

Using a password manager and Diceware, which an earlier post mentioned, are good practices in general, not just on Tor. On some sites, people had attempted to bruteforce passwords, and randomly generating them seemed to help prevent this. Most password managers (e.g. pass, KeePass, Bitwarden, LastPass) have the ability to randomly generate passwords as well. Part of the reason for doing so is that if someone knows you and knows that you like coffee, for example, they may be able to guess that you would use a password like “coffee12345.” The password managers bypass this process altogether.

On Unix and Unix-like systems, the standard password manager is pass, which is command line-based. While it may take some time to learn, pass is relatively simple, and its official site has good instructions as well.
In addition, a lot of sites require using Pretty Good Privacy (PGP) when registering. While PGP itself has security issues, it does work reasonably well as a method of verifying someone's identity, or in the case of Tor, proving that a site is genuine. Often, sites like marketplaces will display their public PGP key on the front page for this reason.

As for creating and storing your own PGP key, there are a number of different PGP clients for different operating systems. On Windows, for instance, the standard PGP client is called Gpg4win (GNU Privacy Guard for Windows), which can be downloaded from Gpg4win – Secure email and file encryption with GnuPG for Windows. From there, the process will vary depending on your OS and the client that you are using, but most are fairly simple.
Every PGP key is a keypair, i.e. a public and a private key. Never share your private key with anyone! The private key is used to encrypt and decrypt messages, whereas the public key is the one used to sign messages and verify your identity, as in the above image.
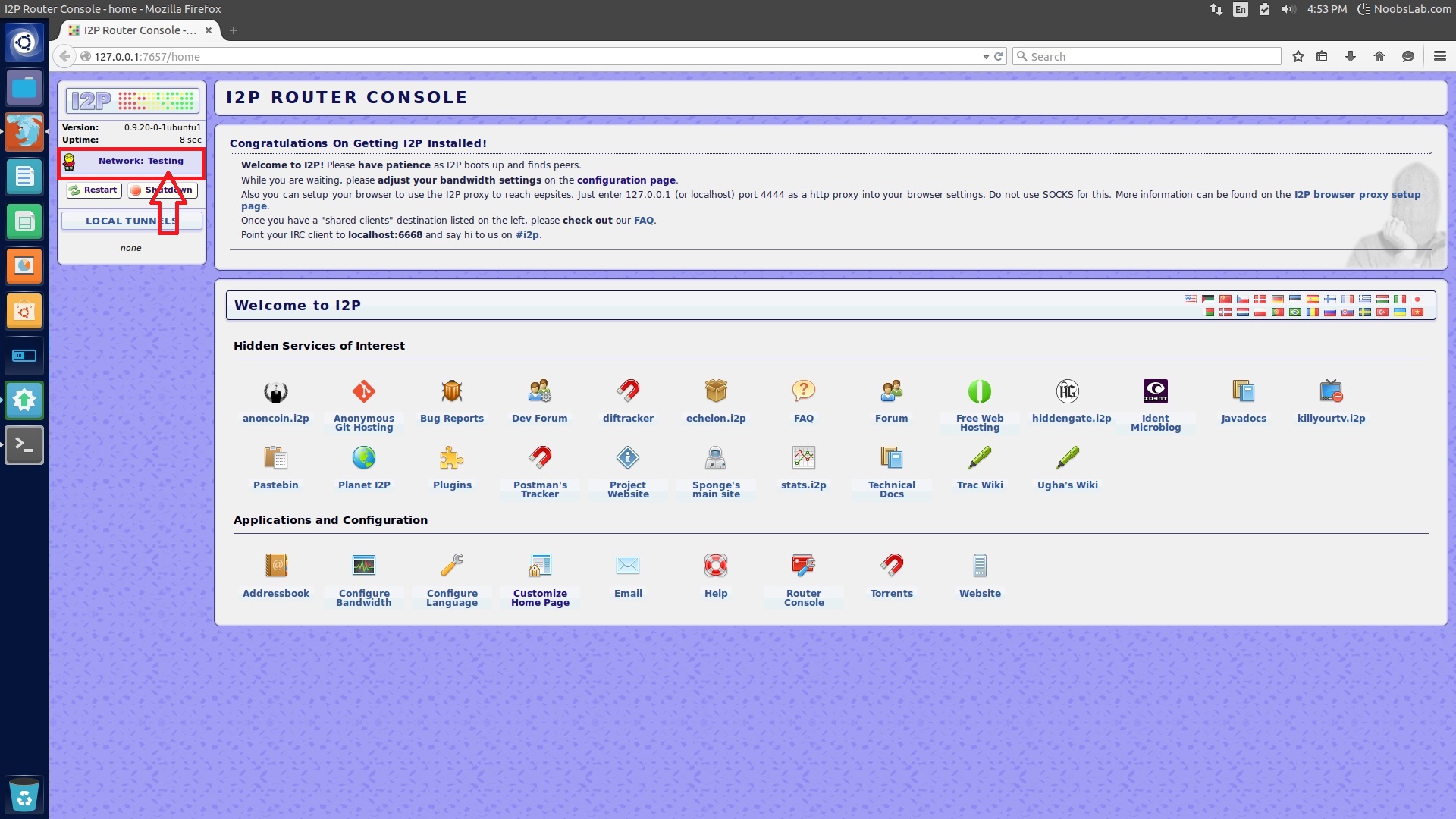
It should be noted that the “dark web” consists of more than just Tor, although in the past few years, the two have become conflated with one another. Tor is merely one anonymity network that falls under the dark web umbrella. Other such networks include I2P, Freenet, GNUnet, and Oxen (formerly known as Lokinet). These other networks are all considered to be “anonymous peer-to-peer (P2P) networks, in which the nodes are anonymous or pseudonymous.
As far as staying “safe” on these other networks is concerned, the same rules apply as those on Tor, in a sense: you can still use the random password generation methods as above, but on networks like Freenet, that may be unnecessary. Freenet, like PGP, uses keypairs (public and private), and the network's sites, known as “freesites,” consist of part of the sites' public keys. Your identity, when you register, also has a corresponding keypair; it is important, therefore, that you keep your private key safe, just as you would with your private PGP key.
Some of the potential danger with Freenet and other P2P networks comes in with the filesharing aspect: you do not necessarily know if the files you are downloading are safe; there will be other posts about this in the future to go into further detail.
There are probably other precautions you can take as well, but some of the learning process just comes from experience. Just be skeptical of everything you see, and if something looks suspicious, it is best not to get involved with it.