What are Some Alternatives to ProtonMail?
Those who keep up with privacy news have probably heard about ProtonMail handing over the IP addresses of some of its users to Swiss law enforcement in the recent case, prompting a lot of criticism from those in the community.
If you read the article above, however, ProtonMail says they were forced to comply with the order and could not appeal. Their suggestion to users was to use their Tor hidden service, which also obfuscates IP addresses in a way that ProtonMail itself cannot.
There are, of course, other email services that are similar to ProtonMail, in that they are (ostensibly) privacy-focused, but no email provider can be trusted 100%, unless you set it up yourself. People have discovered the same issues regarding VPN providers that claim not to keep logs as well, particularly in cases when law enforcement subpoenaed them to hand over a user's data.
Part of the issue is that email, in general, is not the most secure form of communication, as email messages are easy to intercept. A post on StackExchange explains some of the reasons behind this:
Emails can be sniffed in transit, since they are not encrypted (some sites will opportunistically employ encryption for transit, but this is not reliably activated).
Emails will be stored on physical disks in the servers which are involved in the operation: the sender's email server, the recipient's email server, and any server “in between”. Physical disks can be sniffed when decommissioned or through backup tapes. Bored interns in the facilities managing these servers could simply have a look.
It is easy to make emails go to the wrong machine by altering the DNS.
There are viruses which routinely inspect emails received by infected machines, in search for passwords, credit card data or other juicy information.
The whole email system just assumes that everybody is honest and nice and trustworthy. It is surprising (but morally encouraging) that it works at all.
A similar situation occurred with a provider named Hushmail back in 2007, and the Reddit post Hushmail: A cautionary tale of trusting webmail providers like Protonmail summarizes this situation a bit:
Before Protonmail or Tutanova [sic], or whatever the flavor of the month 'secure' webmail snake oil provider is, there was Hushmail, which similarly offered “secure” and “encrypted” webmail, claiming that “not even a Hushmail employee with access to our servers can read your encrypted e-mail, since each message is uniquely encoded before it leaves your computer”.

And then court records showed that Hushmail handed over several CDs-worth of emails to the US (Hushmail was based in Canada):
On June 6, 2007, DEA SA Shawn Riley received three CD'S via Fed Ex from the DEA San Diego Division Office. The CD's were the results of a mutual legal assistance treaty (“MLAT”) executed on Hush Communications Inc, based in Canada, for email addresses [Hushmail email addresses]. Hush Communications Inc., also known as Hush Mail, is a free encrypted email communication system that claims to ensure the security, privacy, and authenticity of emails sent and received by it's users.
The results of the MLAT conducted on [Hushmail email address] included an IP log associated with access to this e-mail account.
In the same sense as putting your trust in a VPN provider, you are relying on a third party to protect your data, even if they claim to have a “privacy-centric” or “anonymous” service. Additionally, the mere fact that a company advertises itself as being more private usually makes it a target for attackers.
Still, better options exist: sn0w, admin of the Pleroma instance cofe.rocks, suggested encrypting emails with PGP, as well as using either Mailbox or Posteo.de, part of the reason being that although they are paid services, they accept anonymous forms of payment and support features like PGP.
Mailbox.org offers such features as an email account, online office, cloud storage, video conferencing, etc. While it is paid, as opposed to providers like Gmail, it is still inexpensive, and the fact that it relies on payment means that they do not have to serve you with ads in order to make money (unlike Facebook, for instance).
It has become a habit as of late to read a company's privacy policy before signing up with any of their services, so here is the one for Mailbox.org: Data protection & privacy policy. While some of these can be lengthy and full of legalese, it can prove helpful to know what kinds of data they collect from you, especially if you are wanting to avoid a fiasco like those of some of the big tech companies.
Mailbox.org also has a free 30-day trial for those who want to test out the service, which is enticing, to say the least. You can compare it against some of the other email services (e.g. ProtonMail) to see how they fare in terms of privacy and usability. It is encouraging to see that Mailbox receives A+ grades on three of the major “security checkers”: Qualys SSL Labs, DANE SMTP Validator, and CryptCheck.
Sn0w also made the point that both Mailbox and Posteo have the option to reject insecure inbound/outbound connections for extra security:
Posteo help: Activating TLS Sending Guarantee
Posteo help: Activating TLS Receiving Guarantee
Mailbox.org: Ensuring E-Mails are Sent Securely
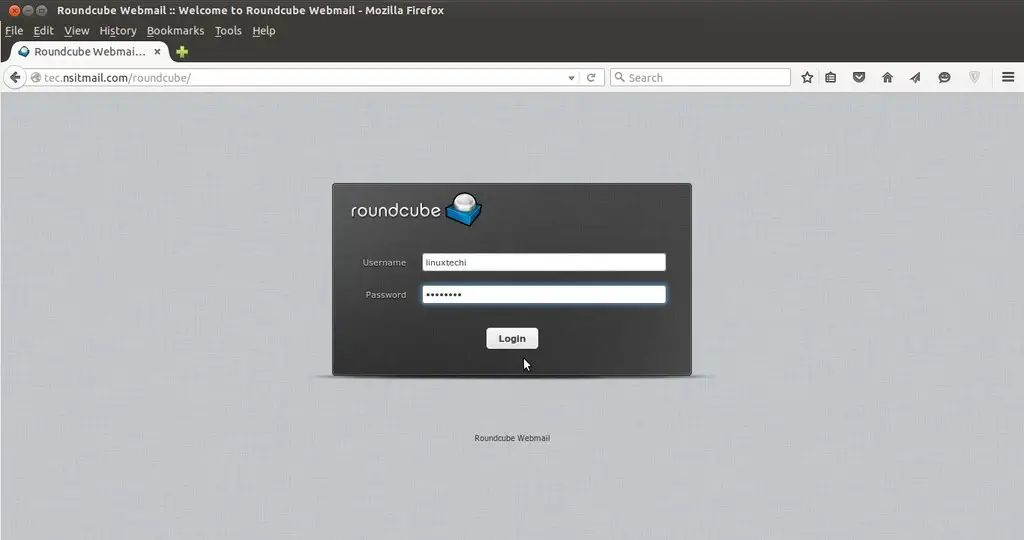
Speaking of which, Posteo, which is based on the open source Roundcube. Roundcube is also the basis for Riseup and several other email providers.
Like Mailbox.org, Posteo is ad-free, although the account requires a paid subscription; it is inexpensive, though. The account only costs 1 EUR ($1.13) per month, which, in terms of tech subscriptions, is a fair deal (compare that to some VPN provider subscriptions, for instance)!
Some of its features include:
- 2 GB of storage, increasable up to 20 GB (for a higher price)
- Attachments up to 50 MB
- Email on all devices
- Spam and virus filter
- Two alias addresses
In privacy terms, Posteo says that it keeps as little data about its customers as possible, which is reassuring, especially after fiascos like that of Protonmail. You can read their privacy policy to be sure: Posteo Privacy Policy.
Posteo is also not financed by advertising, unlike a service such as Google – hence the subscription fee.
Many people still make the “nothing to hide” argument when discussing privacy online, i.e. “Why do I need privacy tools? I have nothing to hide.” Yet, in many cases, these same people will change their minds when they find out that their information was included in a data breach or something similar. It is more likely that those who make this argument are not aware of how much data is available about them on the web, or who might be after it. This is why it is good to peruse privacy policies, and also to be aware of how personal data and accounts can be compromised (and the answer to that is “in many ways”).
If you know of some other good pro-privacy email providers, please feel free to suggest them! There will be more articles about tools such as this in the near future.